Conceal Threat Alert: Chinese Threat Actor Targets Users in WhatsApp
A recent white paper by researchers at Cyjax uncovered the activities and infrastructure of a financially-motivated Chinese threat actor abusing trusted brands in WhatsApp links to perform a variety of malicious actions, such as delivering malware and malicious advertising. They labeled the group Fangxiao.
Fangxiao stands apart from other criminally motivated groups because of the sheer scale of their attacks. One of the strategies uses to stay anonymous is to rapidly iterate through domain names. In one case, they used over 300 in one day. In fact, the researchers uncovered more than 42,000 domains used by the attackers since 2017.
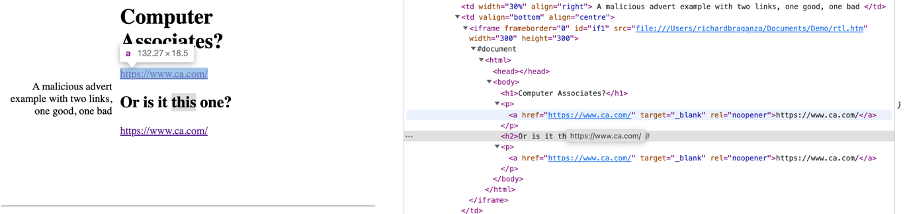
These domains mimicked domains of legitimate companies in a variety of verticals and several countries. The attackers send links to users in WhatsApp that specify a brand the corresponding landing page should impersonate. This allows Fangxiao actors to tailor messages to any brand they think is likely to be effective for a particular audience. The brand is passed to the landing page, which is then automatically customized to mimic the brand in question to build trust with the user. The page is further customized based on the user’s location to show local currency units to appear local regardless of what country they are visiting from. Like the Disneyland Malware Team we wrote about previously, the success of the attack hinges on the users’ trust of the brand overcoming any suspicions they might have about the link.
These extra touches are meant to keep the user engaged with the site and garner trust. They are taken through a journey that results in them providing their friends’ WhatsApp numbers so the attack can be spread to their contacts, downloading malicious software, and generating affiliate revenue for the attackers.
How Dynamic Remote Browser Isolation and Phishing Protection Can Stop These Attacks
The fact that the Fangxiao actors utilize WhatsApp links as the initial attack vector highlights a growing trend in Internet usage: While many attacks happen in the browser, the plethora of communication and other apps containing web links means that email-based phishing and malware protection isn’t enough. Regardless of how a malicious URL reaches a user, the attack happens in the browser. That’s why ConcealBrowse checks every URL being opened in the browser, regardless of where the user clicks it.
ConcealBrowse uses up-to-the-minute threat intelligence – including about newly-registered domains that haven’t even been used yet – to determine which are risky so that they can be opened in an isolated environment, off your endpoint and off your network. Additional phishing protection then identifies fraudulently-branded web sites and prevents users from providing any data to them or interacting with them.
Try ConcealBrowse for free, or schedule a demo so we can show you how ConcealBrowse provides phishing protection and malware protection against threats like Fangxiao.
Written by: Conceal Research Team